Mobile SSL vpn timeout
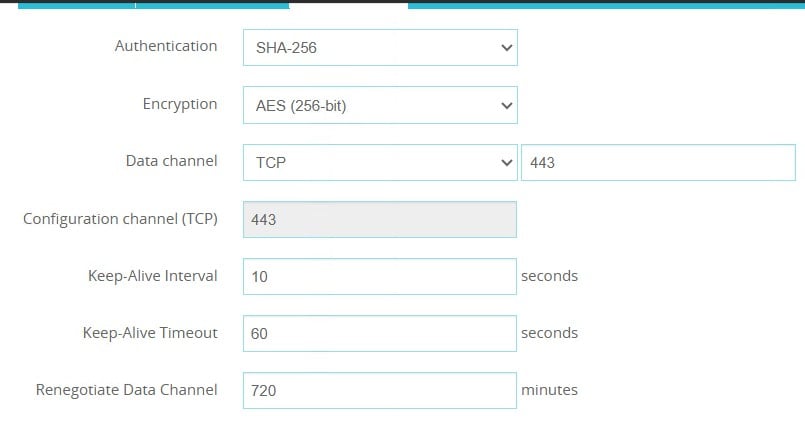
Hello, I'm having an issue with our M390 boxes. Mobile SSL VPN users are being disconnected around the 8 hour mark even though we have the Renegotiate Data Channel set for 720 minutes. I think it started happening when the Access portal was disabled (by us) a a couple of releases ago.
I dont have logs right now as it was just brought to my attention but its the same on all 3 of our M390 boxes.
We are running version 12.11.8. Is there a second place when I need to increase the timeout settings for Mobile SSL VPN? Any help will be greatly appreciated!
0
Sign In to comment.
Comments
There is no normal timeout for SSLVPN connections, given the Keep-alive setting.
What authentication type is being used for SSLVPN users?
Using SAML ?
We using Active Directory for authentication. So the renegotiate Data Channel doesn't have to do with how long it keeps the SSL connection active for the user?
Clearly there is something else causing your issue.
Are you using MFA for SSLVPN?
From the docs:
If a Mobile VPN with SSL connection has been active for the amount of time specified in the Renegotiate Data Channel text box, the Mobile VPN with SSL client must create a new tunnel.
But this does not mean to me that the session should end.
And in your case the Renegotiate time is > 8 hours
Do you have Automatically Reconnect selected on the client ?
Yes, I think most users do have Automatically reconnect selected. I read on a different threat that it may have something to do with the AccessPortal time out or something but we have the portal disabled
Consider opening a support case on this.
Thank you
I was able to get some log entries a a user that was kick off today.
2026-03-27 16:40:07 Deny 70.170.194.114 95.160.70.205 https/tcp 5278 443 External Firebox tcp syn checking failed (expecting SYN packet for new TCP connection, but received ACK, FIN, or RST instead). 222 121 (Internal Policy) proc_id="firewall" rc="101" msg_id="3000-0148" tcp_info="offset 5 A 2617256773 win 65535"
2026-03-27 16:40:50 Deny 70.170.194.114 95.160.70.205 https/tcp 5275 443 External Firebox tcp syn checking failed (expecting SYN packet for new TCP connection, but received ACK, FIN, or RST instead). 40 120 (Internal Policy) proc_id="firewall" rc="101" msg_id="3000-0148" tcp_info="offset 5 AR 3770166597 win 0"
2026-03-27 16:40:22 Allow 172.24.4.210 172.24.5.1 dns/udp 61324 53 tun0 Trusted Allowed 63 127 (Allow SSLVPN-Users-00) proc_id="firewall" rc="100" msg_id="3000-0148" src_user="smitho@orgent.com" record_type="A" question="forum.netgate.com"
2026-03-27 16:40:51 admd Authentication of SSLVPN user [smitho@orgent.com] from 70.170.194.114 was accepted msg_id="1100-0004"
2026-03-27 16:40:51 sslvpn Mobile VPN with SSL user smitho logged in. Virtual IP address is . Real IP address is . msg_id="2500-0000"
2026-03-27 16:40:53 sslvpn Mobile VPN with SSL user smitho logged in. Virtual IP address is . Real IP address is . msg_id="2500-0000"
2026-03-27 16:40:53 sessiond SSL VPN user smitho@orgent.com from 70.170.194.114 logged in assigned virtual IP is 172.24.4.204 msg_id="3E00-0002"
2026-03-27 16:41:02 Allow 172.24.4.204 172.24.5.2 dns/udp 52357 53 tun0 Trusted Allowed 61 127 (Allow SSLVPN-Users-00) proc_id="firewall" rc="100" msg_id="3000-0148" src_user="smitho@orgent.com" record_type="A" question="wpad.ccculv.com"
2026-03-27 16:41:05 Allow 172.24.4.204 172.24.5.2 dns/udp 62406 53 tun0 Trusted Allowed 61 127 (Allow SSLVPN-Users-00) proc_id="firewall" rc="100" msg_id="3000-0148" src_user="smitho@orgent.com" record_type="A" question="wpad.ccculv.com"
2026-03-27 16:41:05 Allow 172.24.4.204 172.24.5.2 dns/udp 56420 53 tun0 Trusted Allowed 62 127 (Allow SSLVPN-Users-00) proc_id="firewall" rc="100" msg_id="3000-0148" src_user="smitho@orgent.com" record_type="A" question="mtalk.google.com"
2026-03-27 16:41:09 Allow 172.24.4.204 172.24.6.7 rdp/tcp 52787 3389 tun0 Trusted Allowed 52 127 (Allow SSLVPN-Users-00) proc_id="firewall" rc="100" msg_id="3000-0148" tcp_info="offset 8 S 3854701619 win 65535" src_user="smitho@orgent.com"
2026-03-27 16:41:09 Allow 172.24.4.204 172.24.6.7 3389/udp 57399 3389 tun0 Trusted Allowed 1260 127 (Allow SSLVPN-Users-00) proc_id="firewall" rc="100" msg_id="3000-0148" src_user="smitho@orgent.com"
2026-03-27 16:42:31 sessiond SSL VPN user smitho@orgent.com from 70.170.194.114 logged out assigned virtual IP is 172.24.4.210 msg_id="3E00-0004"
2026-03-27 16:42:31 sslvpn Mobile VPN with SSL user smitho logged off. Virtual IP address is 172.24.4.210. msg_id="2500-0001"
2026-03-27 16:43:18 Allow 172.24.4.204 172.24.5.1 dns/udp 52357 53 tun0 Trusted Allowed 76 127 (Allow SSLVPN-Users-00) proc_id="firewall" rc="100" msg_id="3000-0148" src_user="smitho@orgent.com" record_type="A" question="dns-tunnel-check.googlezip.net"
2026-03-27 16:43:18 Allow 172.24.4.204 172.24.5.1 dns/udp 56420 53 tun0 Trusted Allowed 66 127 (Allow SSLVPN-Users-00) proc_id="firewall" rc="100" msg_id="3000-0148" src_user="smitho@orgent.com" record_type="A" question="tunnel.googlezip.net"
2026-03-27 16:43:19 Allow 172.24.4.204 172.24.5.2 dns/udp 63404 53 tun0 Trusted Allowed 67 127 (Allow SSLVPN-Users-00) proc_id="firewall" rc="100" msg_id="3000-0148" src_user="smitho@orgent.com" record_type="A" question="whatismyipaddress.com"
From a Google search:
tunnel.googlezip.net is a Google-owned domain associated with Chrome's "turbo net" or Private Prefetch Proxy service. It speeds up browsing by compressing data and preloading pages. While not a virus, it can cause high, unexpected traffic on websites, leading some to block its IP addr
and:
To disable prefetch in Chrome, navigate to Settings > Performance, find the Speed section, and toggle off Preload pages. This prevents Chrome from preloading pages it thinks you might visit, saving network bandwidth and memory
Not sure if any of this is related to your issue
I think I found the place I need. I set it for 13 hours, now its just a waiting game to see if it works.